Data security is a follow that can not be ignored in what you are promoting operations. This follow includes a sequence of steps to guard enterprise info from unauthorized entry resulting in cyber assaults (cyber crime) and knowledge loss. For you, the proprietor of an organization or retail enterprise, an understanding of information safety is the important thing to sustaining the continuity of what you are promoting.
On this article, Cloudeka will present an entire assessment of information safety. We’ll additionally share enchancment tips about knowledge safety and implement it in what you are promoting. Learn this text till the top so you possibly can perceive extra absolutely about knowledge safety.
Understanding Data Safety
Information safety refers back to the follow of defending knowledge from unauthorized entry and injury. This follow contains the whole lot from worker info to buyer transaction knowledge.Information safety is not only about holding knowledge secure, but additionally guaranteeing that knowledge will not be altered or accessed by unauthorized events.
Information safety works by figuring out potential threats, then securing knowledge with encryption and different safety strategies, and monitoring suspicious exercise. Within the course of,knowledge safety includes a wide range of applied sciences and practices designed to guard knowledge from a wide range of dangers.
Information is probably the most worthwhile asset for an organization. If firm knowledge is leaked or stolen, this may trigger main monetary losses and even threaten enterprise continuity. The principle factor is,knowledge safety is a element that can not be ignored in constructing info safety and defending firm belongings. Subsequently,knowledge safety is a vital element for the continuity of what you are promoting.
Types of Data Safety
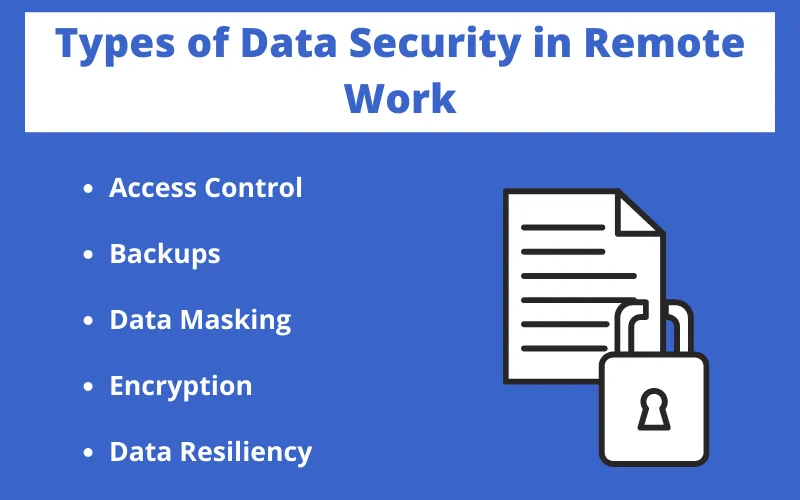
Deep follow knowledge safety divided into several varieties with their respective working strategies, specifically:
1. Data Encryption
Information encryption is a knowledge safety method that makes use of algorithms to transform knowledge right into a format that can not be learn by unauthorized individuals. That is performed utilizing encryption keys which solely licensed events learn about. This method is an efficient approach to shield delicate knowledge throughout transmission and storage.
2. Firewall
Firewall is the primary line of protection in opposition to cyber assaults.Firewall is a safety system used to observe and shield laptop networks from exterior assaults.Firewall works by blocking suspicious entry by way of a technique of analyzing incoming knowledge and figuring out undesirable exercise.
3. Entry Control
Entry management is a safety method used to regulate entry to knowledge and programs. This course of is carried out by granting entry permission solely to licensed individuals.Entry management used to limit entry to file, folders and functions from unauthorized individuals. You’ll be able to management who can entry knowledge and programs and restrict undesirable entry.
4. Backup and Recovery
Backup and restoration is a safety method used to create copies of essential knowledge that may be recovered within the occasion of information injury or loss. Subsequently, it is very important create backup and restoration knowledge periodically. It will make sure that essential knowledge will not be misplaced and may be recovered if injury happens in order that what you are promoting continuity is maintained.
5. Intrusion Detection System
Intrusion Detection System is a safety system used to detect exterior assaults and supply warnings to community directors.Intrusion Detection System works by analyzing community site visitors to detect undesirable exercise and take crucial actions to forestall assaults. This method may also assist determine community vulnerabilities and enhance its safety.
Cloud Database vs Traditional Database: Migration for Modern Business Success
6. Authentication
Authentication is a safety method used to make sure that the individual accessing knowledge or a system is a licensed celebration and their credentials are recorded in database the system.Authentication includes the usage of passwords, entry playing cards, or different authentication strategies.
7. Data Loss Prevention (DLP)
DLP is a expertise that displays and prevents knowledge leaks. DLP ensures that delicate knowledge doesn’t leak out of the corporate. With DLP, firms can determine, classify, and shield their most beneficial knowledge.
8. Endpoint Safety
Endpoint safety protects finish gadgets akin to computer systems and smartphones from cyber assaults.Endpoint safety comes within the type of antivirus and safety software program malware. Endpoint Safety can also be used to observe finish system exercise and detect indicators of assault. With robust safety on finish gadgets, you possibly can make sure that all entry factors to your community are secure from malicious cyber threats.
Benefits of Data Safety for Business Continuity

Information safety is one thing that can not be ignored in enterprise. Why? Listed below are the advantages of information safety.
1. Protect Important Data
Firm knowledge is an asset that can not be changed. Information safety protects this worthwhile info from injury or loss. This implies that you could safely keep the continuity of enterprise operations and make sure that essential info will not be misplaced in sudden conditions.
2. Maintain company productivity
With safe knowledge, companies can function with out disruption brought on by cyberattacks or knowledge loss. Secure and uninterrupted productiveness is a vital facet for sustainable enterprise progress, and knowledge safety is the principle basis in attaining it.
3. Prevent Cyber Attacks and Data Loss
Information safety helps stop cyber assaults which may injury enterprise operations and trigger vital knowledge loss. By implementing correct safety measures, you possibly can keep away from the prices and losses that may end result from a harmful cyberattack.
4. Prevent Unauthorized Access to Business Data
By controlling entry to knowledge, you make sure that solely licensed individuals can view and use enterprise info. This not solely protects knowledge but additionally supplies a way of belief to clients, enterprise companions and stakeholders that you simply take severely your duty to take care of the confidentiality of knowledge.
5. Increase Customer Confidence
Clients can have extra belief in firms that may safeguard their knowledge nicely. This actually improves the picture and belief of consumers. This fashion, they may really feel comfy doing enterprise with you, sharing private info, and persevering with a long-term enterprise relationship.
6. Maintaining Business Reputation
Information loss or cyberattacks can injury a enterprise’s repute.Information safety helps keep repute within the eyes of consumers and enterprise companions. Information safety is an funding in sustaining a optimistic picture of your organization in an more and more aggressive market.
How to Implement Data Safety on a Company Website?

Web site The corporate is a worthwhile asset and must be protectedknowledge safety. So, apply knowledge safety on web sites? The next is the reason.
1. Using Secure Socket Layer
Safe Socket Layer (SSL) is a expertise used to encrypt connections between server and browser. With SSL, delicate info akin to buyer knowledge and transaction info will likely be strongly encrypted, in order that unauthorized events can not peek or steal the info. This is a vital first step in sustaining buyer confidence within the safety of your web site.
2. Conduct a Security Review
Finishing up common safety critiques is a proactive step to make sure that firm programs and knowledge stay secure. On this assessment, the IT safety group will consider potential vulnerabilities, verify compliance with the newest safety practices, and consider adjustments that could be wanted to enhance safety ranges. That manner, you possibly can determine potential dangers earlier than they develop into severe threats.
3. Ensure the connection used is encrypted
Encrypted connections are an essential a part of knowledge safety, particularly when clients make transactions in your web site. Be sure that all info despatched and acquired by your website is encrypted utilizing robust safety protocols such asSSL/TLS. This fashion, you possibly can present assurance to clients that their private info is secure throughout their go to.
4. Using a Firewall
Firewall will not be solely essential on the community stage, but additionally on the utility stage and web site. Be certain that the web site is protected by a firewall to discourage assaults that might threaten knowledge integrity and availability.Firewall will monitor each request coming out and in of your website, checking for indicators of suspicious exercise, and robotically blocking suspicious entry. This fashion, you possibly can shield your knowledge from doubtlessly damaging assaults